Could apps be stealing your data? These little things that sit on your phone and obediently do your biding, is there a chance these mobile apps could be exposing your personal information to anyone on the world wide web? Yes! There’s a chance.
If you use a lot of apps, there’s a possibility that you could accidentally download a malicious app that steals data. It is also plausible that even the reliable apps that you use could fall victim to a data breach, thereby leaving you vulnerable. In either scenario, safeguarding your privacy on mobile apps is important.
- Within the first half of 2021, there have already been 1767 reported incidents of data breach, exposing a total of 18.6 billion records.
- Financial records, bank correspondences and sensitive financial documents of up to 38 million people were exposed in the Automatic Funds Transfer Systems (AFTS) attack.
- More than 220 million Brazilians were affected in a major data leak that exposed automobile registration numbers, personal tax identification numbers, birthdays, full names, headshots and much more.
- Moreover, average cost of a data breach continues to rise. 2021 had the highest average cost of data breach in 17 years, rising from USD 3.86 million to USD 4.24 million.
While the good app developers out there are doing everything they can to protect your privacy online, there are a few steps that you – the users – can take from your side, to protect your privacy.
As you can clearly see, data breach is a big problem. It leaves very sensitive information like full names, address, photos, social security numbers, personal banking information and much more, leaving you vulnerable to a large number of threats.
So it’s time to become aware and gang up against these threats. The good news is that most attacks can be warded off if you are a little extra careful with everything you do on your phone.
In fact, financial and personal information is just the tip of the iceberg. Data leaks and privacy infiltrations on mobile apps can have much bigger consequences. When Aspire News App, an app made for victims of domestic abuse, suffered a data breach in June 2020, extremely sensitive information about thousands of domestic abuse victims was exposed.
Mobile app developers are continually striving to make their apps ironclad against privacy attacks, and downloading trusted apps only can help you stay safe most of the time. For the rest, there are several steps that you as a user can take to stay safer and more secure while using mobile apps. Let’s have a look at how you can protect your privacy online.
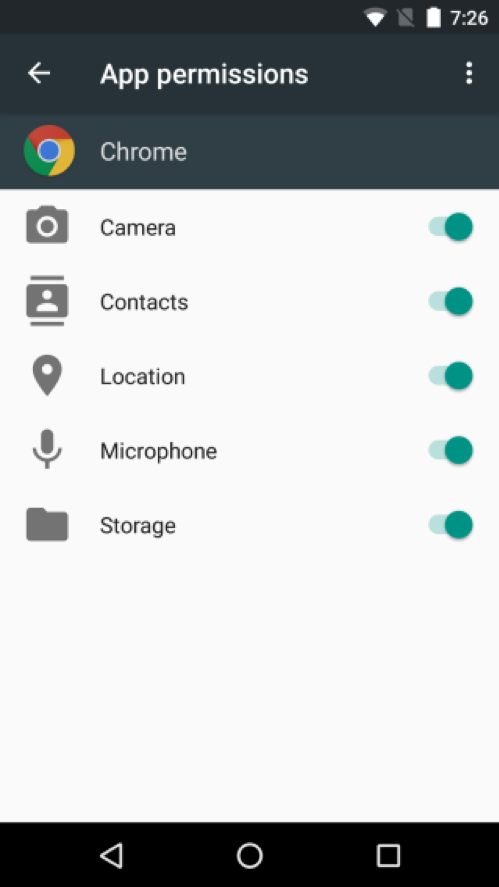
1. Careful with the app permissions
Most mobile apps you install begin by asking a bevy of permissions. The most common ones include using your location, contacts, messages, photos, camera, and call records. Other apps also ask for more intrusive permissions, practically giving them access to everything you read, write, view, search for or talk about. All of these pieces of information become susceptible to data breaches.
It is almost muscle memory. We click on install app, it asks for permissions and our finger just hits allow.
It’s time to get more cautious about these permissions. Pause for a moment and look at what permissions an app is asking for. Why does this app need access to your text messages? Why does it need to access your photos? Do you really want to give it GPS location access? Maybe you can just ballpark around your city address.
When it comes to app permissions, it’s important that you become aware of what you are allowing an app to do on your phone. Give only the most essential permissions that you feel particular app must have. If you find a long list of permissions, remember to check all those boxes that you do not want to allow access to.
This step, though fairly simple, can be the most discerning factor in preventing most apps from accessing your personal data.
If it so happens that you simply cannot move forward with the app without giving it all the permissions it is asking for you probably have enough reason to be suspicious of this app. It might be a wise decision to uninstall this app and look for an alternate option in the App Store. And that brings us to our next point.
2. Only trust reliable app stores
More than a decade ago, Apple launched something called an App Store and our lives changed forever. Google followed suit and launched its own app store. Today, there are plenty of other app stores to choose from including the Windows App Store, Samsung App Store and many more. There are in fact, several other app stores that are increasingly becoming popular are publishing apps that do not find a spot on these mainstream app stores or that appeal to smaller developers thanks to their better profit sharing policies.
However, it would be in your best interest from a privacy standpoint to stick to the most popular app stores that belong to trusted companies. Quality and credentials of apps on smaller app stores could be questionable and so are their privacy and security policies.
Downloading your apps exclusively from the Apple or Google app stores does provide you at least some security against attacks knowing that these app stores follow a rigorous quality check before publishing any app on their platform. The same also applies to app stores of companies like Samsung or Windows to quite a large extent.
Many other smaller app stores on the other hand could possibly be allowing some not so secure apps fall through the cracks. This is not to deny that alternate app stores often have some very useful apps available sometimes even apps that you cannot find on the mainstream app stores. If you must download apps that you can only find on these alternate app Stores, take some time to perform a thorough background check of the developing company and the publishers. Check out the reviews and ratings of the app and look for some credibility before you download an app on your mobile phone. As far as possible, it is a safe practice from a privacy and security standpoint, to download your apps from the mainstream App stores.
3. Enable remote wiping
One of the most obvious privacy concerns is what happens to our data if we lose our phones. One of the most important things you can do to prevent losing your data upon losing your phone is to enable remote wiping of all the data on your phone. For instance, when you buy a new iPhone, you are required to sign up for an iCloud account which becomes the primary command centre of all the information on your iPhone.
If you ever lose your iPhone, you can remove all the data just by signing into your iCloud account from any device. Anybody who manages to break into your iPhone still doesn’t get access to any of your information once you have invited.
Similar options are easily available in android as well as other phones. You can even download certain apps that would allow you to remotely wipe your data from your phone. It is always a good idea to utilise one of the services in case you ever lose your phone.
4. Don’t automatically social sign in
Sure it is the age of fast food and quick services. Everything we do needs to happen in a moment. When an app gives us the option to sign in using our social network settings that we have already saved in our phones, it sure saves us the trouble of typing an email addresses and phone numbers all over again.
However, saving those few minutes could cost a lot more in the future. Signing into an app using the social media can you give an app the access to our social accounts which some apps could completely abuse. They could get access to your personal information, your photos, your memories, your contacts and so much more.
This makes social sign in a potential privacy threat and something you shouldn’t do unless you completely trust the app. Using an email address and unique password to sign in is undeniably the best way to use an app. If this is the kind of app that you share sensitive information with, setting up a phone number and using an OTP for important decisions can also be a good idea.
5. Use a password
This might sound like a no-brainer but yet it just so happens that most people still do not use a password to unlock their devices. A survey by consumer reports shows that 64% of users don’t use a password. Sure you need to use your phone 1 million times a day and having to enter a pass code every time can be a bit of a hassle.
However when it comes to your privacy and security is completely worth it. These days, a mobile phone is a one-stop access to your home address, your travel plans, your money and pretty much everything you do.
When you are practically walking around with your life’s savings in your pocket, are you really satisfied with the convenience of unlocking your phone in a swipe? Take a moment, enter a password. Your fingerprint could also be an easy security step your phone has that feature.
A word about pattern lock here-if you come to think of it, they might not be the best security measure to keep outsiders outside your phone. If you paid attention, phone screens are suckers for fingerprints. If you use a pattern lock several times a day, you have likely used it recently, and have left a mark on the screen that anyone can easily see simply by touching your phone in the sunlight. So once again, choose a fingerprint and a passcode over a pattern lock and above everything else, remember to use the past or at all.
6. Choose your apps wisely
For some of us, downloading new apps can be just as exciting as shopping. That explains the urge to download every new app and check it out. However, it would be a good idea to be more selective with the apps that you will have on your phone.
Considering how much information you save on your phones on a daily basis, allowing an app on your phone is like allowing a person into you are home. If it looks even slightly suspicious, better of keeping it outside the door.
Before you download any app, is the time to thoroughly study and do your homework. Find out more about the developers of this app. Is it a reputed company, do they have enough stars in good reviews, how long have they been in the business, Do they have any major complaints against them in the past.
You can get access to most of this information from the developer page on app stores I am some more by running a check on them even on Google. Some knowledge better than no knowledge try to find out what you can about the credibility of each app you allow on your phone. The good thing about app stores is that they are brimming with Apps. There are over 3 billion apps on the App Store is today so you could easily find another app just like the one you were hoping to download kind of suspicious.
7. Beware of public Wi-Fi
Using a public network to access apps on your mobile phone also exposes you to a number of a vulnerabilities. Sitting at an airport or a cafe with free public Wi-Fi and sometime to kill could automatically mean that you reach out for your phone and click on one of the apps.
However, public Wi-Fi is home to a number of attackers and malicious software. This does not mean that you never use public Wi-Fi. It only means that you are discerning about what you do and what you don’t on a public Wi-Fi network. If you wish to check out latest news orphan some of your favourite coffee table designs, go right ahead.
However, if you are looking to buy a pair of shoes order groceries when you get home, you might want to wait until you actually get home. Shopping apps have your credit card information and using them on a public Wi-Fi is not such a bright idea.
8. Update your apps
Even the apps that you trust and regularly use can sometimes end up with bugs in them. The best App development companies are constantly on alert for these removing them as soon as they are found.
Your job here is to continually update your apps so that any bugs that accidentally got your name can be fixed and your apps remain in tiptop shape the simple act of updating your apps can help you keep your phone secured and your data.
It’s also a good idea to delete the apps that you no longer use. Point to keeping apps on your phone even when you don’t use them, not only from the storage point of you but also for your privacy.
Wrapping up
Those are some of the simple yet very important steps each of us can take to keep our data protected when we use mobile apps for our everyday uses. It is hard to ignore just how much will depend on apps. Everything from shopping and banking to working, playing, and keeping in touch with our family, happens on mobile apps. As a result, these apps can access some of our most private information and is compromised, can easily be a source of disaster. That is why it is immensely important that we remain vigilant about what we share with mobile apps as well as what apps we allow on our phones.
The single step of being selective about the apps we download can be one of the biggest steps we take to protect ourselves online. Tap development companies know the risk involved in letting your data be hijacked, stolen or sold. As a result, they build their apps using the best technology and approved privacy and security practices to ensure that your data stays safe. Add to that some of the above steps we talked about and you can safely go on using your mobile apps without worrying about just where your data is being shared.